-
Ürünlerimiz İnceleyin
Taşıt Kabloları, Marine Kablolarımız, Marine Kordonlarımız ve daha fazla ürünlerimizi buraya tıklayarak ulaşabilirsiniz.
-
Fiyat Listesi
Güncel Fiyat Listemizden Haberdar Olmak İçin Tıklayın.
-
Bize Ulaşın
Firmamız Hakkında Daha çok bilgiye ulaşmak için bize ulaşın.

Ürün Teknik Data
Hakkımızda
Bizi Yakından Tanıyın
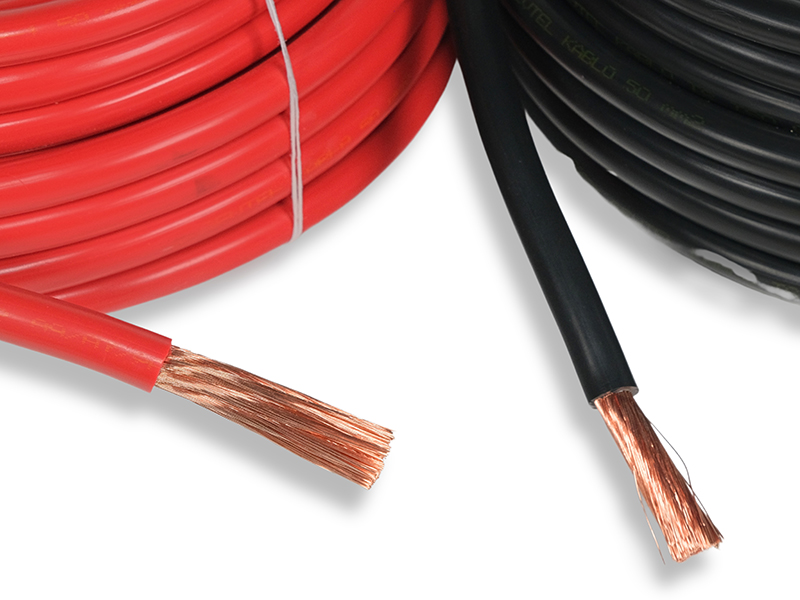
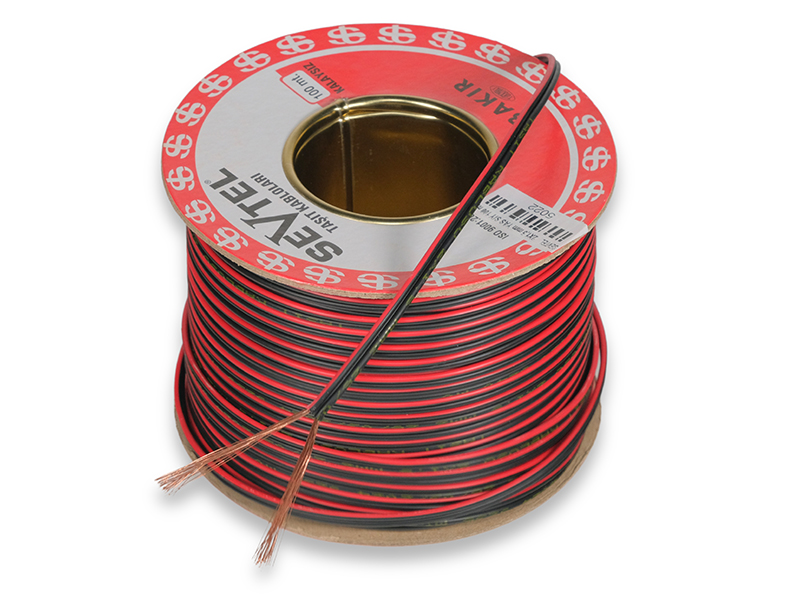
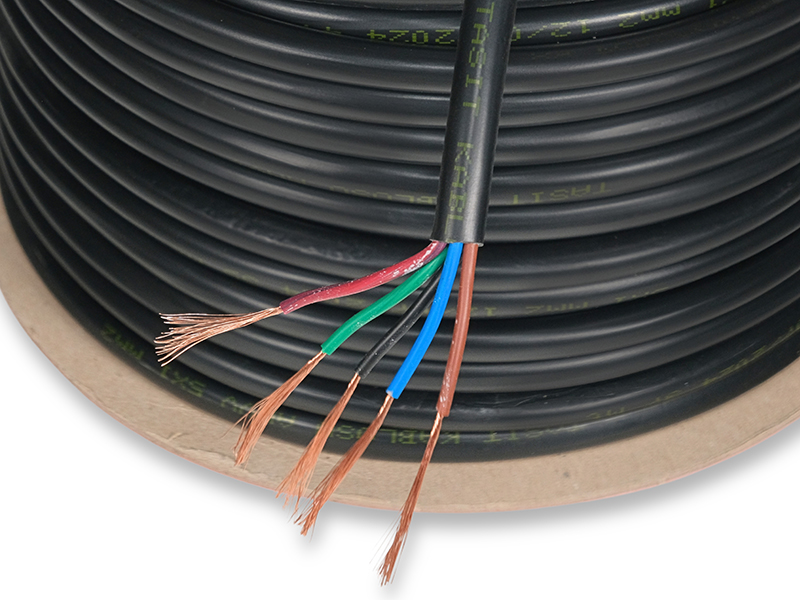
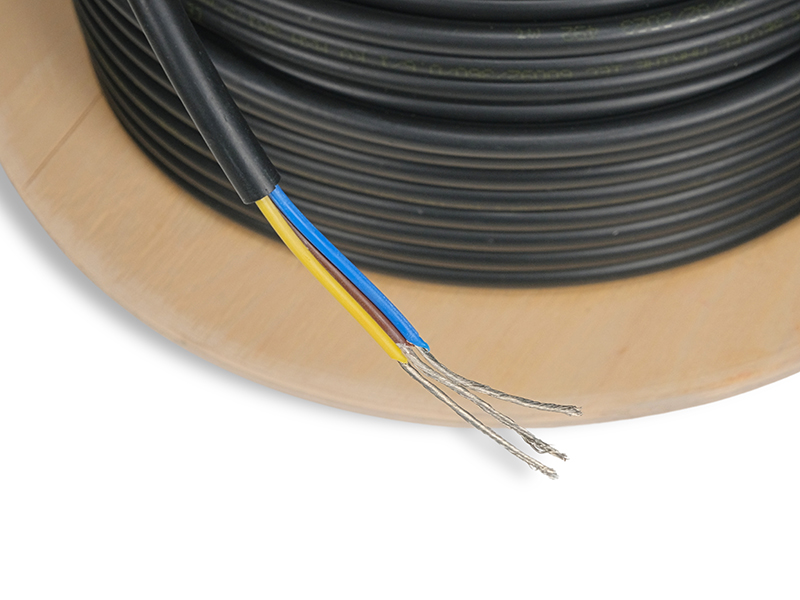
TAŞIT VE MARİNE KABLO(MYY-MX-MXH-MHH-MXCH) 1977 yılında taşıt kablosu üretmek üzere Hüsnü SEVİM tarafından İstanbul'da kurulmuştur. Firmamız 1984 yılında TSE kalite belgesini almış, iç piyasada kalitesi ve 45 yıllık ticari tecrübesi ile güvenilir bir marka olmuştur. Bir aile şirketi olan firmamız, Varol SEVİM tarafından yönetilmektedir. Firmamızın en önemli özelliği tek telefon ile firma sahibine ulaşarak her türlü soru ve sorunlarınıza en kısa yoldan cevap alabilmenizdir.Daima sektörde öncü bir firma olmuştur. Kağıthane-Seyrantepe de 2,000 mt2 kapalı alanda imalat yapmaktayız. Taşıt Kabloları : ISO 6722-01 (PVC) TSE BELGELİ Marin Kablolar: IEC 60092-360/350 MYY MX-MXH-MHH-MXCH RİNA ve TURK LOYDU Sertifikalı Kaynak Kablolar: CE belgelidir
Tümünü Göster


Soru, öneri ve görüşlerinizi iletmek için, bu numaradan +90 212 281 72 15 hafta içi saat 08.30-16.00 arasında bize ulaşabilirsiniz. Cumartesi Pazar çalışmamız yoktur